DocFraggle Indeed!
Ok, so with the reject line commented out, it does show a match in rspamd, nothing in postfix (expected?).
So the question is, by adding this blocklist, how does it work with the rest of the postscreen spam filtering. If the connecting ip is already blacklisted on those indexes (spamhaus and others);
In general, past behavior with such bad actors would result in a reject like this.
NOQUEUE: reject: RCPT from [35.197.0.99]:45836: 550 5.7.1 Service unavailable; client [35.197.0.99] blocked using zen.spamhaus.org; from=<>, to=<name@domain.com>, proto=ESMTP, helo=<[10.88.0.3]>
If these other filters are catching it ahead of this one, then the only real benefit may be if bad ip is on the bitwire list but hasn’t made it to the other blacklists. It still spams the log with the connection attempt vs being blocked from connecting in the first place.
Also, there’s a memory component involved. Not a big deal if instance has lots of ram. Results from top, before and after using this list.
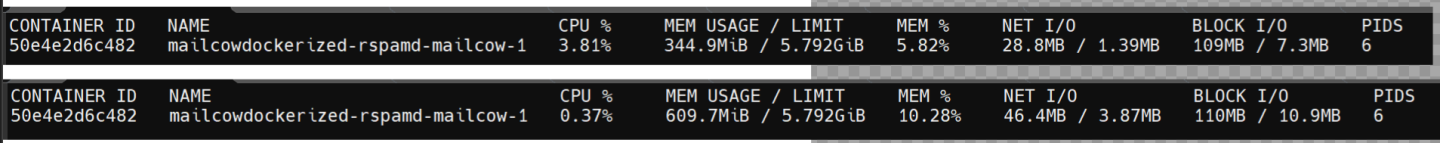
About a 265MB increase for the container. Ram usage does fluctuate so these are approximations. Small price to pay if it’s useful.