Hi, I recently moved my mailcow instance to a new VPS so it runs independently from other services.
The new VPS is behind a firewall that I want to use to block spam traffic before it reaches the VPS.
I added all the required (TCP) rules for incoming traffic to the VPS. There is no outbound filtering rule, so outbound traffic is not filtered at all.
Example:
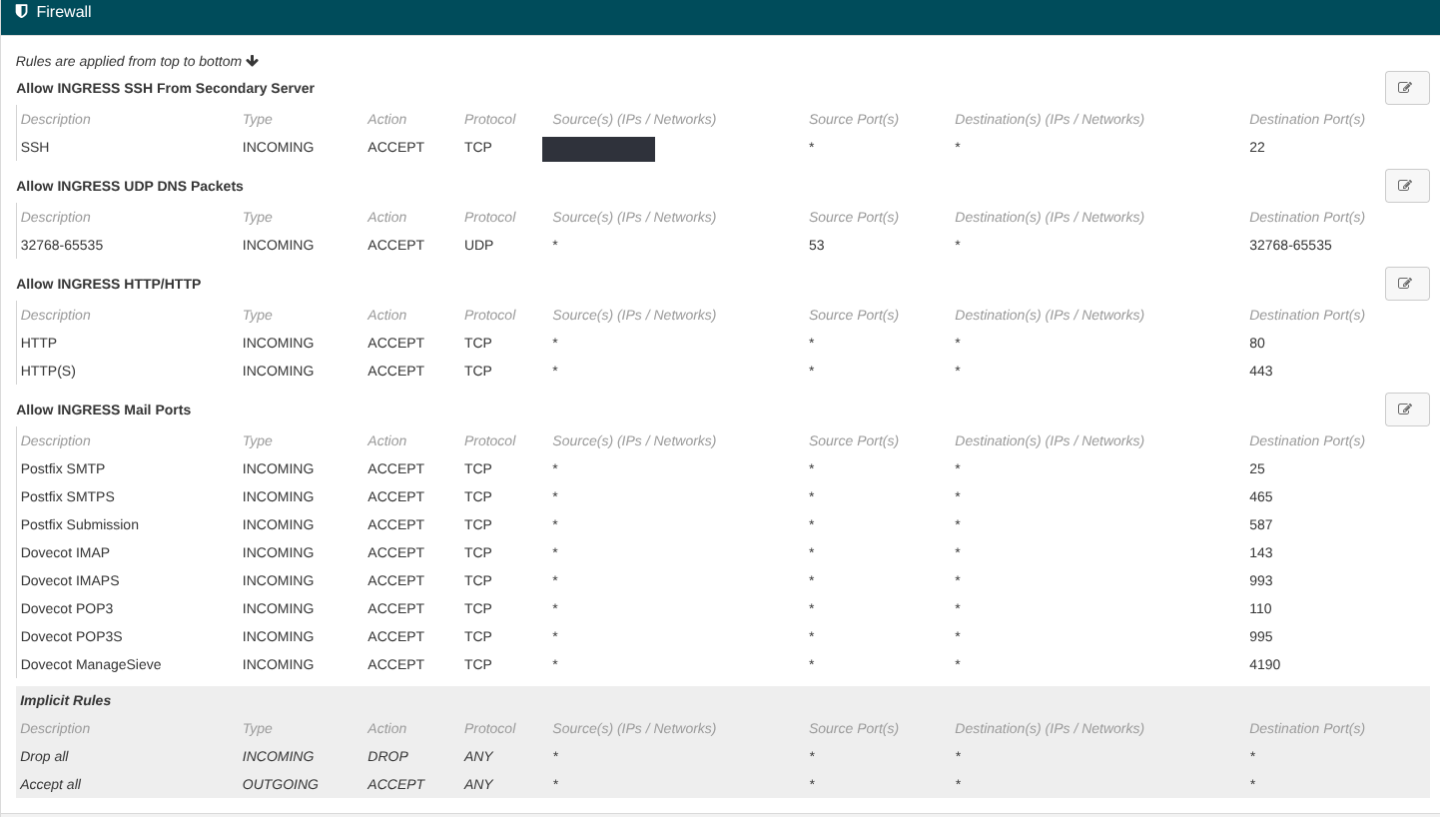
However, mailcow-unbound sends DNS queries over UDP to the internet, and because of UDP being stateless the firewall doesn’t know that it should allow those UDP packets back in and thus blocks them.
I see two possible solutions:
1) Which I currently use:
Allow incoming UDP traffic with source port 53 to the UDP ports used by Unbound (see https://docs.mailcow.email/getstarted/prerequisite-system/#important-for-hetzner-firewalls).
The downside of this being a lot of open ports, which I wanted to avoid as much as possible.
2) Use a local DNS resolver (for example the VPS provider’s resolver) and forward queries to it (see https://docs.mailcow.email/manual-guides/Unbound/u_e-unbound-fwd/).
Using method 2 with the override/forwarding method skips Unbound, so my understanding is that DNSSEC validation would no longer be performed by Unbound. Is that correct?
3) Using the Override config from 2 combined with a local DNS Resolver running on the Host machine doing the DNSSEC validation and using some other Protocol than UDP for upstream requests.
Which method is the most secure option in your opinion?